1 Executive Summary
Business continuity is the ability of an organization to maintain critical business functions during, as well as after, a disaster has occurred. Traditional business continuity plans consider potential disruptions such as natural disasters, fires, disease outbreaks, and cyber attacks. However, the trend towards digital transformation and an increasing reliance of organizations on IT for critical business functions and data means that cyber attacks are the most likely threat to business continuity. As cyber attacks continue to increase in number and ability to cause significant damage to IT infrastructure, organizations must ensure that efforts to secure IT operations are closely aligned with efforts to maintain/restore IT operations in the event of a cyber attack, with a focus on:
- Risk management;
- Resilience to maintain system and data availability;
- Recovery of systems if they go down; and
- Contingency planning for varying degrees of IT failure, up to and including total IT failure.
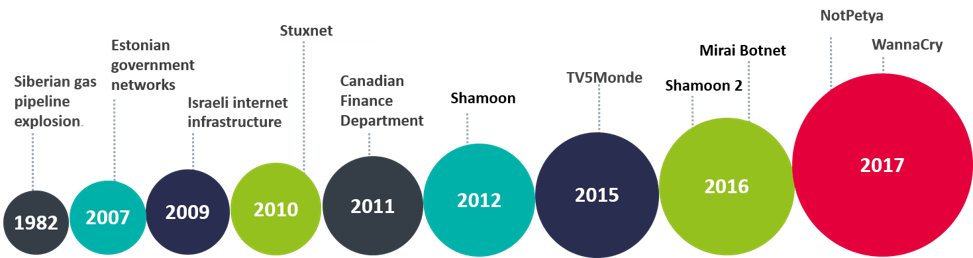
A comprehensive approach has become necessary as attacks by nation states or those supported by nation state level development capabilities become destructive in nature, capable of disabling access to systems and data or even destroying IT infrastructure.
This advisory note outlines the need for a fresh, collaborative approach to Business Continuity and Cyber Security, and some approaches and considerations that will help organizations to limit the initial and short-term impact of cyber attacks on business operations to achieve the common goals of resilience and recovery, including contingency planning for extreme scenarios such as targeted, long-running attacks that might spread across data centers or disable key IT infrastructure.