1 Executive Summary
Internet of Things (IoT) devices are proliferating as more consumers, companies, countries, and organizations embrace Digital Transformation. IoT is at a nascent stage with an ecosystem that is still fragmented and disorganized. However, IoT will play an increasingly important role in how businesses are run and how we organize our everyday lives. So, what exactly is the Internet of Things? It is a concept of connecting any device to the Internet (and/or each other): cell phones, wearable devices, machine components and just about anything you could think of. The IoT is a giant network of connected “things”, including people. The relationship is between people to people, people to things, and things to things.
A “thing” could be a person with a heart monitor implant, a livestock animal with a biochip transponder, or an automobile with built-in transponders, to name a few. IoT has evolved from a convergence of wireless technologies, micro-electromechanical systems, microservices, and the Internet. The convergence has torn down walls between operational technology and information technology, allowing unstructured machine-generated data to be analyzed for insights that will drive improvements.
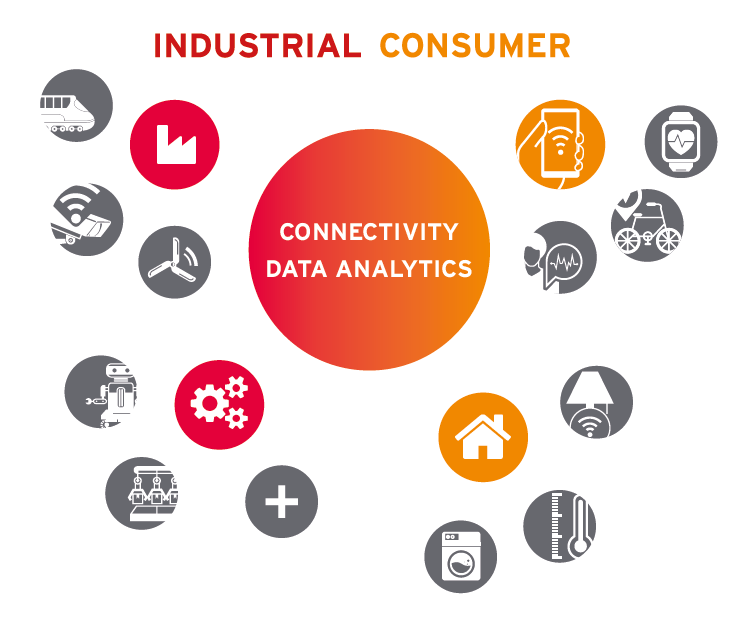
Manufacturing, as an example, has been operating shop floor equipment for decades with sensors that control processes, but these sensors have not been IP-enabled and have not been able to communicate beyond their local process. This is changing: manufacturing equipment is now being produced with smart sensors, that opens up a whole new paradigm known as the Industrial Internet of Things (IIoT).
Like most other Information Technologies before, IoT was not designed with security in mind. Many IoT devices lack the technical capacity to instantiate and execute basic identity management and security practices. Some IoT devices that do have basic identity functions have been so poorly implemented that it makes them easy targets for hackers. Consider the October 2016 attack on DNS service provider Dyn. Using the Mirai botnet malware, an attacker was able to recruit thousands of internet-connected webcams in a DDoS attack to overwhelm Dyn, which led to an outage affecting several major websites, lasting several hours[^1].
Digital identity can play an important role in protecting both IoT devices and the systems with which they interact. Identity is the basis for authenticating and authorizing traffic and data transactions. Without a notion of identity at the device level, the challenges of security administration in IoT connected systems are greatly magnified. By combining device identity management with user identity management, administrators can build profiles and policies to:
- Permit, deny, or limit traffic to/from IoT devices and other networks
- Permit, deny, or throttle data transfers to/from IoT devices and other networks
- Control which users can read data from IoT devices
- Control which users can administer which IoT devices
Authentication and access control at the device level are paramount to securing the devices, their associated data, and even the Personally Identifiable Information (PII) of individuals. Consider the smart health environment, with smart medical devices operated by authorized medical professionals for the benefit of specific patients. For such a scenario to function securely, medical staff must have properly provisioned digital identities, with appropriate entitlements to operate and monitor the smart medical devices. The medical staff need health records of the patients, as well as real-time data feeds from the smart medical device(s). However, the smart medical device generates PII (personal health information in this case), which must be protected according to medical privacy regulations. Thus, building well-designed and robust identity ecosystems encompassing both devices and users is an urgent requirement in IoT.
IoT devices are proliferating, and application platforms for IoT are rapidly being developed. Fortunately, an awareness of the need for identity and security with regard to IoT devices and applications is increasing among the device manufacturers, enterprise customers, and even consumers. This awareness, coupled with advances in IoT device technical capabilities, should eventually result in the creation of more secure IoT systems. This paper examines the current challenges in identity and security for IoT, as well as the nascent developments that preface the possibilities of a more secure future for IoT.










































